Arriving At A Passwordless Future
Look Familiar?
Below is an abridged (and prettier) version of a white paper I’m working on. I outline my reasoning around the password problem, how various existing solutions attempt to solve it (spoiler alert: they don’t!), and finally how passwordless solutions on the horizon might once and for all solve the password problem.
Intro
Passwords suck. They’re incredibly frustrating to use. They’re also incredibly insecure. Stolen and weak passwords accounted for 81% of data breaches in 2017 1. Imagine a world where in order to login, ALL you have to do is push a button - now imagine that world is thousands of times more secure. Let’s walk through how to arrive at that world.
Security Explanation
Here are three common, effective, and widespread attacks against passwords.

Zuckerbook
Brute force attack
A lot of people use weak or easily guessable passwords. For example, there was a huge LinkedIn password database dump. Hackers found Mark Zuckerberg’s email and brute forced his password (essentially tried a bunch of combinations) which was ‘dadada’ 2.
Password reuse
Some people use the same password across multiple accounts, so if one account gets compromised their other accounts are compromised. For example, hackers used Mark Zuckerberg’s ‘dadada’ password to break into his Twitter account and post something 2.
Phishing attack
Phishing attacks are when a bad actor pretends to be someone else to steal your information. For example, there’s a popular lottery scam where people on Facebook pretend to be Mark Zuckerberg giving away money. The scammer can simply ask for a user’s bank account information, and that user is compromised (in an actual example, scammer’s masquerading as Mark Zuckerburg chose ‘lottery winners’ and swindled $1,500 through iTunes gift cards and wire transfers 3).
All of these password problems (and more) are due to the fact that users are tasked with generating their passwords, managing their passwords, and giving it to the proper parties.
Insufficient Existing Solutions
Let’s start with the most common solutions along with their most common defects.
Most Common 2FA (text/email/OTP generators)
First, let’s discuss 2nd factor authentication, or 2FA.
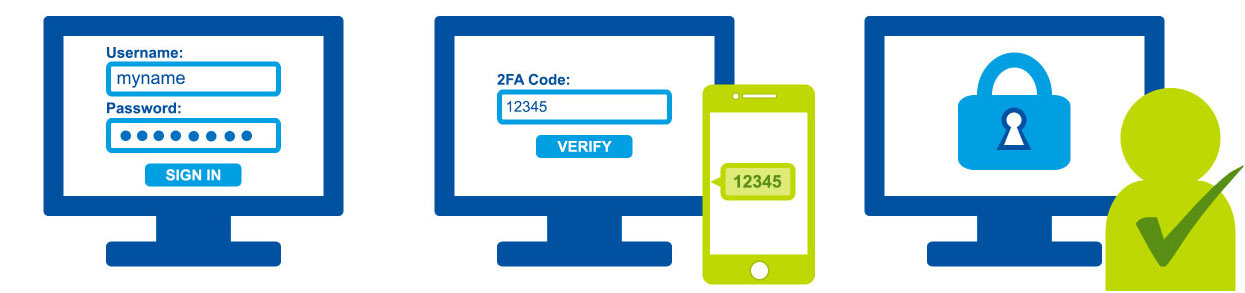
SMS (text) 2FA
The Most common forms of 2FA, such as text message (where you get text a code), email (where you get emailed a code), and one time passwords (called OTPs, for example a device that outputs a code every 30 seconds) are annoying to use and easily phishable. There are additional common attacks, for example someone stole $23.8 million from a cryptocurrency investor through a SIM swapping attack 4, where an attacker takes over a phone number to circumvent text message 2FA, usually through bribing or tricking a mobile carrier (i.e. Verizon) employee.
Passwordless Solutions (insecure)
Now let’s discuss what are called ‘passwordless’ authentication solutions.
Magic Link
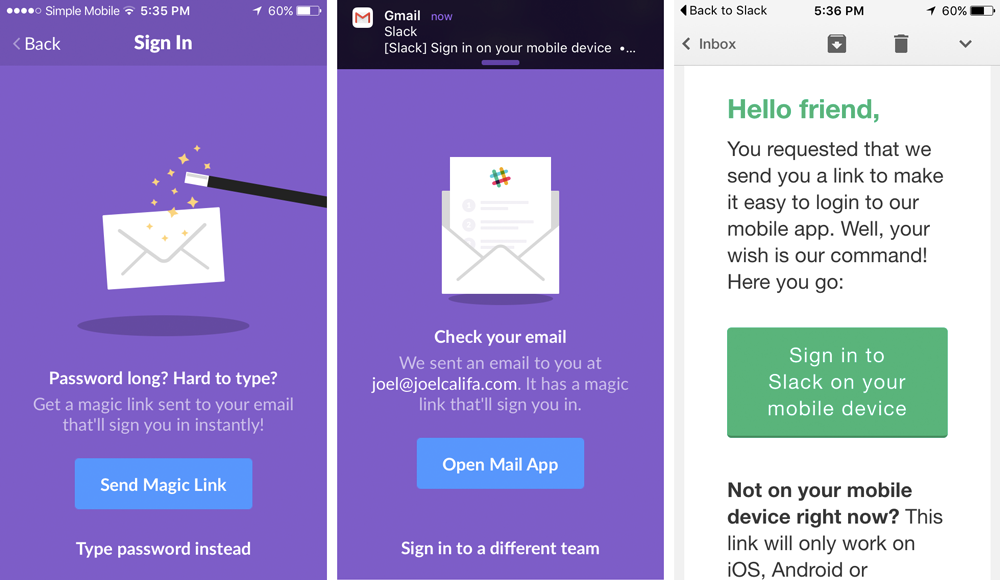
Magic Link (email)
A common form of passwordless authentication uses ‘magic links’. This is where a user gets sent a ‘magic link’ (typically a hyperlink) via email or text message that they simply click in order to login to their account. Like email and text message 2FA, magic links are susceptible to phishing attacks. For example, an attacker could send a legitimate looking email from a legitimate looking address with a malicious link.
One Time Code
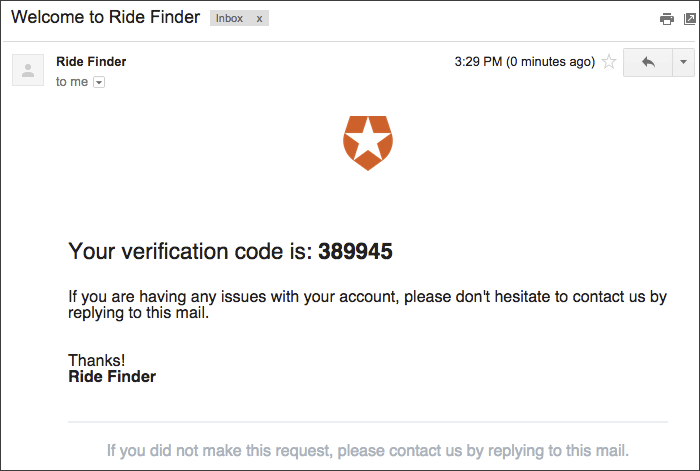
One Time Code (email)
One time code’s are identical to 2FA except they skip the password part. They also have identical security weaknesses and usability issues.
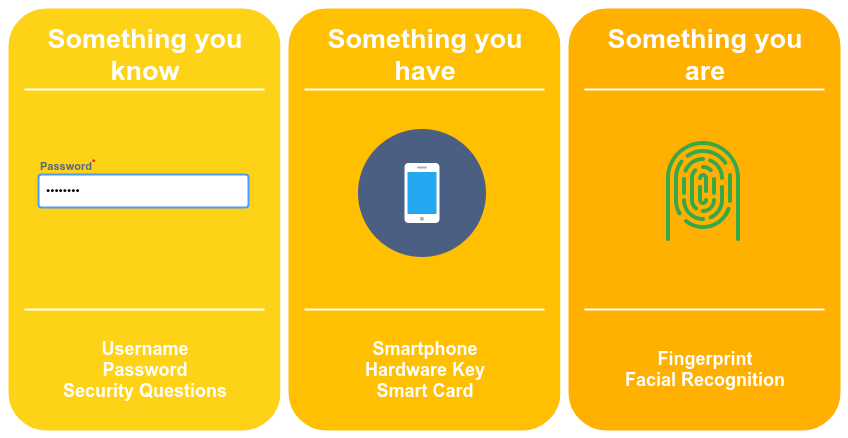
Digital Factors Of Authentication
Authentication Factors
Let’s quickly introduce a concept: digital factors of authentication, or more plainly different forms of logging in. All authentication factors can be broken down into 3 categories: something you know, which is the most common (for example, passwords or pins), something you have (for example a mobile phone or a USB hardware token), and something you are (for example a fingerprint or face biometric).
Technical Insights 1
Our first technical insight so far: a secure and usable digital authentication system CANNOT consist of something you know**. Through passwords we know that humans will generate poor passwords and reuse the same password across different accounts. Through passwords and 2FA/passwordless solutions we know that humans will give up their credentials to a malicious party when phished. We also know through personal experiences that passwords and 2FA are a pain to use. Therefore, in order to have a truly secure and easy to use authentication solution, something you know CANNOT be used**.
Secure Existing Solutions
Now let’s look at password solutions that add genuine security and usability.
Secure 2FA (push notification)

Push Notification 2FA
One secure form of 2nd factor authentication is push notification 2FA, for example the Duo Mobile app. In push notification 2FA, you download an application on your mobile device and tie it to your account. Then anytime you want to log in, you get a push notification on your phone, which opens up the app and asks whether you are trying to login. You push a button to respond, i.e. ‘accept’ or ‘deny’.
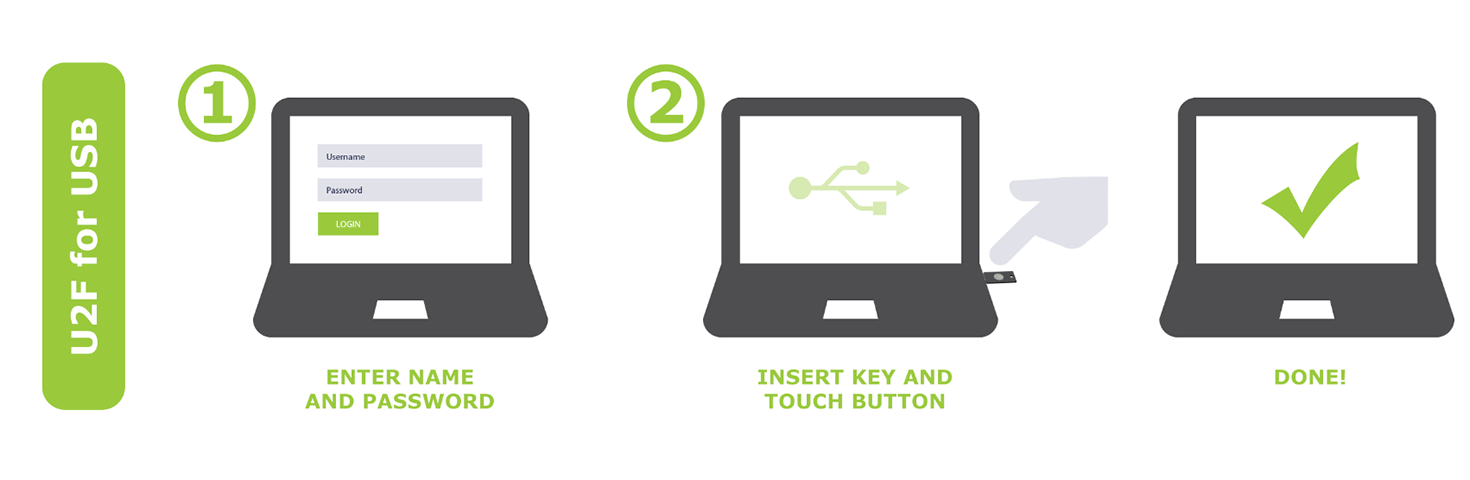
Secure 2FA (security key)
Security Key (YubiKey) Authentication
Another secure form of 2nd factor authentication is security key 2FA, such as with a YubiKey or Google’s Titan Security Key. In this form of 2FA, a user has a separate, dedicated hardware device they carry around with them. After entering their username/password, the user needs to push a button on the security key to confirm logging in.
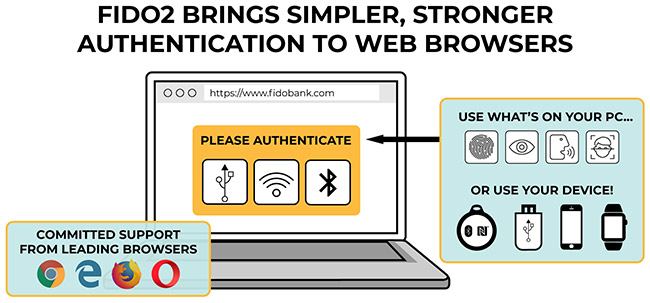
Passwordless Solutions (state of the art)
FIDO2 Diagram
The current state of the art in passwordless authentication is a set of standards called FIDO (currently UAF, U2F, FIDO2 and WebAuthn). FIDO uses a combination of biometrics and some form of trusted hardware to accomplish passwordless login (FIDO also allows for security keys). For example, if you have a banking app installed on your iPhone, it can let you login using Touch ID or Face ID through the FIDO standards.
Technical Insights 2
Notice a common thread between push notification 2FA, security key 2FA, and FIDO - in all 3 cases, in order to login, the user simply needs to perform a gesture. This is our second technical insight: the most advanced login solutions delegate credential management (i.e. creation, provisioning) to a device - a combination of hardware and software - and allow a user to login via a simple gesture (push a button, swipe a slider), which is usually followed by authenticating the user to the device (scan a finger, scan a face using biometrics).
Summary To This Point
Let’s quickly summarize everything so far. Passwords suck. 3 common password attacks are phishing, brute forcing, and reuse. Most solutions to this problem add a layer of inconvenience and marginal security. Push notification 2FA, hardware token 2FA, and FIDO passwordless login add genuine security and ease of use by simply requiring a user to supply a gesture in order to login, while handling the complexities of credential management.
Short Lived vs Long Lived Authentication
Aright, we’re almost there! We just need to wrap our head around one more concept.
There is still one huge, unaddressed, gapping security issue that relates to all current password solutions, and contains another technical insight. There are two types of authentication for any service/application/account - short lived authentication and long lived authentication***.
Short Lived Authentication
Short lived authentication (this can also be thought of as ‘continuous’ or ‘frequent’ authentication) is what you do on a daily basis, for example logging into a banking app or your corporate enterprise account. Short lived authentication provides temporary trust to an account/client pair, so if you log into the Chase app on your iPhone, it temporarily trusts your account on the Chase app on your phone. If you wanted to use Chase through Safari on the same phone, you would need to login again since it’s a different client.
Long Lived Authentication
Long lived authentication occurs much less frequently, and is used to perform account management tasks, for example confirming adding a new device to your account, verifying the new location of a login attempt, or resetting a password. Long lived authentication is tied to an account, which is virtually always an email account. This means all password solutions can be circumvented by compromising the long lived authentication account. Let’s say that again for dramatic effect: even if you have the most state of the art passwordless login turned on for all of your internet accounts, if an attacker breaks into the email account backing your internet accounts, they can reset all of your passwords including your long lived, email account’s****. This means the hacker has essentially hacked into all of your accounts and locked you out, leaving you screwed, donzo, SOL, PWNED, and so on.
Technical Insight 3
This is the 3rd key technical insight - in order to be truly passwordless - in order to seriously enhance security and get rid of the problems associated with passwords, BOTH short lived and long lived authentication need to be completely, absolutely, 100% passwordless.
Solutions
Huzzah! We made it through the password problem, poor password solutions, better password solutions, and 3 technical insights. Now onto the fun part - the solutions. Below are overviews of the most popular theories on what will replace passwords.
2FA Supplants Passwords
There’s one school of thought that passwords are so entrenched (tech debt, everyone’s familiar with them) that they will stick around but become essentially useless, and the main form of logging in will be through 2nd factor authentication.
Centralized Biometrics
Centralized biometrics is where you use a biometric (fingerprint, face) directly to log into all your accounts (think CLEAR from the airport). This is probably the most convenient form of passwordless login (you can’t really lose your face or forget your finger), however security engineers haven’t really figured out how to implement it securely (yet)***** due to two main problems. In computer security, there’s a concept called ‘rekeying’ where you periodically change a user’s ‘security key’. Imagine if a centralized database of people’s biometrics got hacked - you could ‘rekey’ your fingerprint at most 9 times, and you can’t really rekey your face. There’s also serious information leakage issues. Every time you go out in public and touch something or show your face, you leak sensitive login information.
Network Of Trusted Devices
A third possibility for passwordless authentication, and the one I’m working on, is via a network of trusted devices. This may sound complicated but it’s pretty simple. Imagine you have a MacBook and an iPad with Touch ID, an iPhone XS with Face ID, and a Yubikey. After registering the devices to your account, they become trusted, which means any one of them can be used to log you into your account. Let’s go over how this works.
Trusted Device (native authentication)
Imagine you’re on your iPhone XS, and you want to log into your Chase banking app. Instead of Chase asking for your username and password, you type in your username and press login - then your iPhone scans your face, and boom! You just signed into your Chase app using one face and zero passwords! You can imagine a similar flow on your MacBook with Touch ID, where you go to chase.com on Safari, type in your username, click ‘login’, scan your finger, and are successfully logged in (again using one finger and zero passwords).
Untrusted Device (delegated authentication)
There is one issue we need to address: what if you’re on a device that isn’t trusted? There are a number of reasons why you might not want to register a device to your account, for example the device doesn’t have a biometric scanner (i.e. a gaming console like an Xbox), or it’s a shared device (i.e. a hotel computer). In these cases, the untrusted device would ‘use’ one of your trusted devices to log you in. For example, imagine you’re on vacation without your computer, but you need to login to your corporate account. You go to the hotel’s shared computer, navigate to your company’s website, type in your username and click ‘login’. You get a notification on your phone asking if you’re trying to login to a computer in Hawaii. You click yes, scan your face, and boom! You’re logged into the untrusted hotel’s shared computer using your face on your trusted cell phone.
Fin
Passwords suck, but there’s hope. While existing solutions to passwords leave a lot to be desired, there are exciting solutions on the horizon. It’s probably unreasonable to predict exactly how logins will play out, but a passwordless future is looking more and more likely.
Notes
* whenever you see the word ‘authentication’ you can just think ‘login’
** there is one caveat to this rule when trying to login through a biometric on a device and the biometric ‘check’ fails enough times, your phone might prompt you for your password. In properly implemented authentication systems this is not an issue since the password you are using to login to your phone is NOT the credential being used to log you into your account.
*** parts of this are referred to as the ‘account recovery’ or ‘password reset’ problem
**** for some accounts this might be a slight oversimplification - in the real world, there are account recovery flows, but most of those use weak forms of authentication such as security questions (easily guessable/searchable) or use email/text message one time codes (as discussed previously)
***** in a closed environment such as an office, or in a system where there’s a supervisor such as the airport (i.e. to make sure someone isn’t wearing a mask), biometrics appear to be sufficiently secure
Citations
- https://www.mcafee.com/enterprise/en-us/security-awareness/verizon-2017-dbir.html [return]
- https://www.telegraph.co.uk/technology/2016/06/06/mark-zuckerbergs-password-was-dadada-what-hope-do-the-rest-of-us/ [return]
- https://www.nytimes.com/2018/04/25/technology/fake-mark-zuckerberg-facebook.html [return]
- https://www.bleepingcomputer.com/news/security/hackers-stole-17-billion-in-cryptocurrency-last-year/ [return]